The present invention provides an encrypted transmission protocol intended for communication, in particular to mobile telecommunications, of encrypted data packets encapsulated by a particular methodology 210 according to the blockchain paradigm 117 and named Transport Encrypted Protocol (TEP) 100. It is an innovative telecommunication protocol in which blockchain technology is applied to cybersecurity, creating more secure and reliable communications.
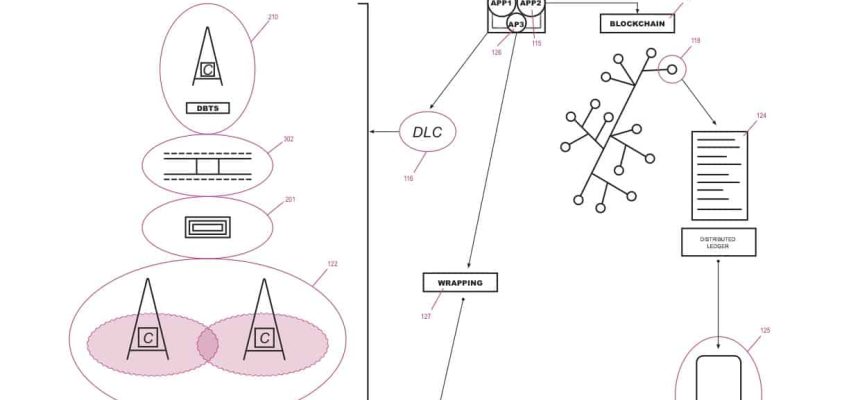
The invention, namely a method, devices, programs and a system for the realization of said protocol, as illustrated in figure n.1 and figure n.5, comprises the following steps:
- the establishment of a distributed ledger based on the blockchain paradigm (117), namely whereas each address is a hash calculated by means of a method of encrypting, such as SHA-512 type, able to generate sender and recipient addresses;
- the establishment of a communication characterized by the encryption of the content to be transmitted and of the channels which transport it, namely characterized by a particular methodology of the encapsulation (210) of the transport layer and of the application level, as defined by the ISO/OSI model;
- the transmission of said encrypted data by means of the selection of an address, namely a destination node also known as hash, with the aim to request a direct send, namely a routing which goes through the minimum number of nodes, thus point-to-point, if sufficiently close, or peer-to-peer type, if the transmission needs to go through intermediate nodes, which nonetheless do not affect the transmission channel, hence they do not store copy of the node data, other than for as long as is strictly necessary to the data transit;
- the receiving of data made by the receiving node, which verifies the integrity of the message and the correct correspondence of the address, decrypts each layer of said particular encapsulation up to the message and hence it decrypts the message;
- the submission of an encrypted notification of receipt to the sender node, namely either an error or a success message, and the subsequent preparation of the receiving node to the next state, namely either the break in communication or, preparing itself to a possible response, the modification of its status from receiver to sender.
The present method further comprises:
- fully digital management of the base transceiver stations (BTS) 101 by means of the use of a particular encapsulation methodology 210 and peer-to-peer technology, which takes advantage of the blockchain 117 paradigm, which transforms the traditional database with a centralized management system into a distributed database 124 which allows each node 118 to interconnect peer-to-peer and simultaneously verify the uniqueness of the customer, thus allowing a communication that is more protected and impenetrable to the main cyber-attacks;
- partial dematerialization of each BTS 101, through the use of a partially dematerialized circuit transceiver apparatuses by replacing the physical component of the circuits with a computer ‘C’ 104 (understood as any type of technology such as, by way of a mere example only, nano-computer, quantum logic fuzzy computers, etc., namely computers able to easily perform the procedural calculation of a circuit simulation) integrated within each BTS (which is thus effectively switched to a Dematerialized Base Transceiver Station ‘DBTS’ 102 ) and powered by the power supplied by the traditional power supply already present in each traditional BTS 101, which is connected to a ‘HV’ 111 hypervisor which, in turn, starts a ‘VM’ 112 virtual machine, which, thanks to the software equipped with its own operating system 113, it allows the management of the Dematerialized Logic Circuit ‘DLC’ 1 16, which, thanks to an application 114:
- the physical government of the antenna of said DBTS 103, namely it communicates the antenna how to create the pulse 201;
- the creation of the digital cryptographic channel 302, which juxtaposed itself, by means of a frequency modulation commutation, to an array of radio frequency analogic channels 303 predetermined by each State on the basis of the geographic area of interest;
- the determining of the manner in which said data encapsulation 210 must be composed so that the recipient can decode data;
- the management of the handover 122 among the mobile stations 125 which use the same TEP protocol 100;
- the creation of several configurations 123 which, by means of the simulation of physical apparatuses, permits to uniquely commutate the communications also to devices and structures, both BTS 101 and mobile stations 125, based on traditional protocols, by ensuring in this way a successful integration between traditional infrastructures and the present TEP protocol 100.
Said operating system 113, present inside the aforementioned virtual machine ‘VM’ 112, also manages, through a specific application 115, the same blockchain 117, which contains the complete database 124 of all caller I.D. and which therefore manages the calls, applying defined criteria to the individual 125 mobile stations, thereby replacing the traditional HLR and VLR.
Finally, a further application 126, installed indifferently inside the firmware 110 of the aforementioned computer ‘C’ 104 or within the operating system 113 contained in the aforementioned virtual machine ‘VM’ 112, carries out the last phase (‘wrapping’) encryption of the data packet using SSL 127 protocol for subsequent transmission via the ‘Transport Protocol’ (TP) 300.
The use of the present TEP protocol, thanks to the features that allow it to be combined with the traditional technology, can be achieved through the progressive implementation of the existing infrastructures with the new technology, becoming itself the supporting technology in the communications sector. In the meantime, the versatility of the instrument can immediately make it spendable, either by integrating the infrastructures with the need for new geographical areas to be covered with the present technology, with greater efficiency, safety and economy; both by replacing the existing BTS where economic reasons, such as those related to the deterioration of an apparatus that can be replaced or repaired, for example by replacing the physical circuit part present in the traditional BTS with the computer described, effectively transforming these BTS into DBTS; or even if strategic reasons, such as the security and impenetrability of a national infrastructure, require it.
This renewal can be carried out gradually and without compromising the functioning of the current data transmission protocols. In fact, thanks to the ability of the software present inside the ‘VM’ 112 virtual machine to create different configurations that simulate existing equipment, it is possible to commute the communications even with the structures that are based on the old protocols (IPX, UDP, TCP / IP), thus ensuring the perfect integration between the old infrastructures and the present TEP protocol.
At the same time, thanks to the radical reduction in size deriving from the dematerialization of the current BTS, the realization of new partially dematerialized BTS (DBTS) will progressively be implemented, which, thanks to the intrinsic characteristics of greater transportability and ease of installation due to the reduced dimensions, will be able to facilitate the spread, throughout the globe, of the TEP protocol even in areas of the planet currently not reachable by traditional wireless technology.
USE AND EXPLOITATION IN INDUSTRIAL AREA
The description provided in this document has the sole purpose of making the possible uses deriving from the exploitation of the TEP protocol comprehensible from a practical and conceptual point of view. It also appears evident to anyone in possession of ordinary skills in this specific area, to understand how the principles enunciated in the present invention can be concretized in numerous other forms and methods.
The TEP protocol has the objective of becoming the world’s standard for communication protocols.
The numerous advantages deriving from its use, first of all the greater security of each transaction (communication), associated with the possibility of implementing this technology in a progressive manner and with minimal economic efforts, guaranteeing total compatibility with traditional protocols, make the implementation and exploitation of the TEP protocol not only advantageous but easily achievable.
The extreme flexibility of the TEP protocol also makes possible its temporary coexistence not only with the current protocols and with the existing network technology (GSM, 3G, 4G / LTE), but also with the future one, as possible implementations of the network standards, such as the 5G network and any subsequent developments.
In this sense, therefore, the TEP protocol has the necessary characteristics to be able to replace, in the short-medium term, the current protocols and, at the same time, effectively manage every future evolution of network technology.
Furthermore, being based on peer-to-peer technology, its use could be extended even beyond the traditional wireless communication systems managed by the single national providers. In fact, the contained cost necessary for its realization, the reduced size of the infrastructures necessary for its realization and the safety deriving from the use of the blockchain paradigm would allow to create secure communication networks for internal use for uses in strategic sectors such as, for example merely illustrative:
- Military and Defense;
- Diplomatic and consular circuits;
- Aerospace;
- Avionics;
- Naval;
- Major works;
- Shipbuilding;
- etc.

0